Security experts globally are starting to rally following the ransomware attack on corporate and private computers last week. What lessons can we take from this event, and how can we be better prepared for the next attack, which will undoubtedly already be in the planning stages?
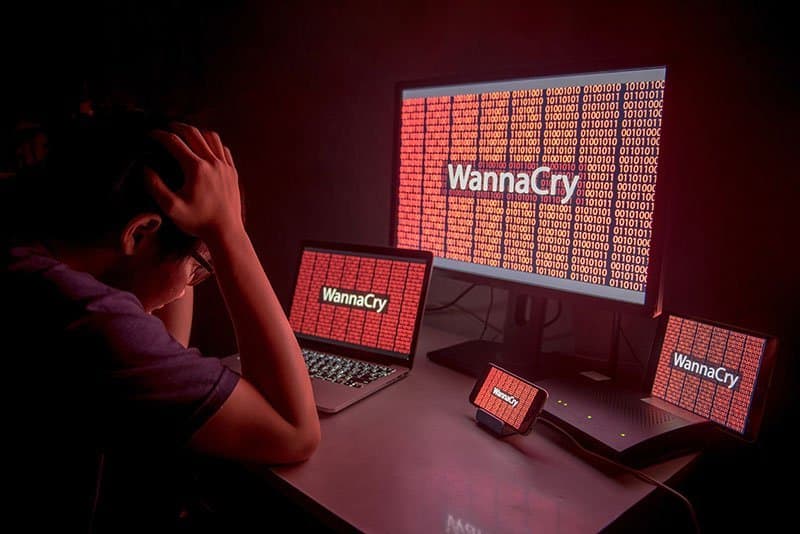
The WannaCry ransomware that has affected more than 230,000 computers in 150 countries now has largely halted its crawl across the globe, but experts at the University of Maryland’s Robert H. Smith School of Business say the attack’s real impact might be yet to come. They predict the assault could herald a turning point in cyber intrusions and in the way institutions handle cybersecurity.
“The damages from the attacks could have easily been avoided had the organizations followed well-known precautions – updating operating systems and installing recent security patches,” says Martin Loeb, Deloitte & Touche faculty fellow, professor and chairman of the Department of Accounting and Information Assurance at the Smith School. He co-authored the Gordon-Loeb Model for Cybersecurity Investments with Smith School colleague Lawrence A. Gordon, EY alumni professor of Managerial Accounting and Information Assurance.
The attack exploited known vulnerabilities in an older version of Microsoft Windows – vulnerabilities that could have been blotted out with recent patches. Now the widespread attack is exposing “the underinvestment in cybersecurity by many organizations,” Loeb says.
This could be one of the lasting legacies of the WannaCry attack, says Sandor Boyson, research professor and co-director of the Supply Chain Management Center at the Smith School.
“When you don’t do the patching and versioning, you don’t get the full protection and full spectrum of defense against vulnerabilities that companies have become aware of,” says Boyson, who for nearly a decade has advised the National Institute of Standards and Technology on cyber supply chain risk management. “Patching and versioning deficiencies are a big problem.”
Experts say remiss patching helps explain why institutions in China, where pirated software is more prevalent, were harder hit than in some other parts of the world. Chinese state media said the ransomware struck nearly 40,000 institutions in that country, including government agencies, banks, schools and information technology firms.
Loeb and Gordon have spent 18 years warning companies to reconsider the amount of money they devote to cybersecurity issues, increasing allocations in some cases and distributing money more efficiently in others.
“These two concerns lie at the heart of the Gordon-Loeb Model for cybersecurity investments,” Loeb says. The model, developed with research support from the Smith School and the National Security Agency, is explained in this video.
Of course, ransomware, such as the kind deployed by WannaCry, is not new. Attacks like these have been increasing in frequency in recent years. But no attack has spread so widely before. The WannaCry hackers were said to have demanded $300 ransoms from affected users, payable in the bitcoin digital currency. Sums paid worldwide appeared this week to be relatively modest, in the tens of thousands, not the millions or billions. But the ransoms were being paid, raising the spectre other attackers will try the same thing.
“We have seen these kinds of threats mutate into something far less benign,” Boyson says. Sometimes, a hacker decides the single ransomware payment is not sufficient, so they write a code that allows them to attack the computer again, demanding another payment, in what’s called an advanced persistent threat.
“The big problem is we don’t see the incentives in place for a lot of change yet, either at the legislative level, the regulatory level or the legal insurance level,” Boyson says. “We don’t really see a converging set of incentives that would drive behavior.”
But that could change, Boyson says, as attacks like WannaCry gain global attention.
Visit Smith Brain Trust for related content at http://www.rhsmith.umd.edu/faculty-research/smithbraintrust and follow on Twitter @SmithBrainTrust.